Apple executive Craig Federighi described a new location-tracking feature for Apple devices at the company's Worldwide Developer Conference keynote called Find My.
The new Find My feature will broadcast Bluetooth signals from Apple devices even when they're offline, allowing nearby Apple devices to relay their location to the cloud. The idea is that you can locate your stolen laptop even when it's sleeping in a thief's bag. It is using everyone else's iPhone to spy on yours – what could possibly go wrong?
Apple insists that it built the feature on a unique encryption system carefully designed to prevent precisely that sort of tracking—even by Apple itself.
"Now what’s amazing is that this whole interaction is end-to-end encrypted and anonymous", Federighi said at the WWDC keynote. "It uses just tiny bits of data that piggyback on existing network traffic, so there’s no need to worry about your battery life, your data usage, or your privacy."
The solution to that paradox, it turns out, is a trick that requires you to own at least two Apple devices. Each one emits a continually changing key that nearby Apple devices use to encrypt and upload your geolocation data, such that only the other Apple device you own possesses the key to decrypt those locations.
As staggeringly complex as that might sound, Apple warns that it's still a somewhat simplified version of the Find My protocol and that the system is still subject to change before it's released in MacOS Catalina and iOS 13 later this year.
However, security experts have warned that the real security of the system will depend on the details of its implementation and while it makes sense on paper, implementing this will be pretty impressive.
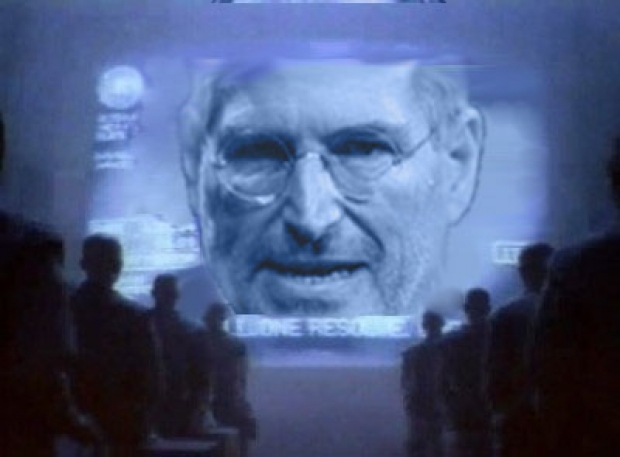
The Tame Apple Press claims that you should trust Apple to get this sort of technology right. After all it's super complicated, cutting edge and pioneering. Given these are the same people who can’t programme a clock to handle summer time, we are not holding our breath. In fact, on Apple's previous form, we are assuming that there will be one basic flaw in the system which will be used to leak information to all the phones in the nearby area. Either way, it is a risk and to take that risk you have to trust Apple.