Boffins at Intruder.io found that more than 40 percent of the FTSE 100, are affected by little-known user enumeration flaws in a range of popular Microsoft products.
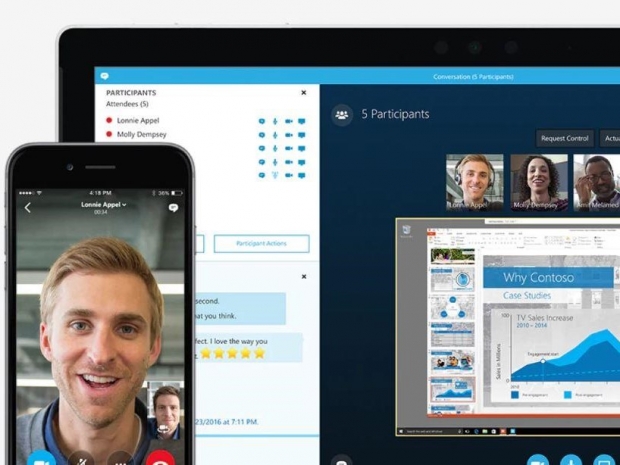
The research uncovered that over 13,000 Skype for Business servers on the internet are vulnerable, potentially exposing an organisation’s internal Windows network to Denial of Service (DOS) and credential guessing attacks.
Among the list of vulnerable servers are household names and large organisations whose high profile make them likely targets for remote attackers. These include numerous blue-chip companies, some of the ‘big four’ professional services firms and UK government-owned domains. The flaws have been exposing internal corporate networks to attacks for years and despite being informed of the vulnerability, Microsoft has no plans to fix the bugs. This leaves organisations without the usual patch/upgrade option that is often the best solution to fixing security issues.
Chris Wallis, Founder and CEO at Intruder.io, said: “Reconnaissance is an essential stage in every attacker’s kill-chain. Companies are facing an increasing challenge to counter the rising numbers of attacks, and anything that makes the attacker’s life harder is worth fixing. It should never be assumed that software is secure out of the box in its default configuration, and our research illustrates how many companies are exposed to unnecessary risk. Easy-to-use tools are publicly available to exploit vulnerabilities, so attacks against these commonly exposed technologies can be carried out even by unskilled attackers.”
User enumeration flaws provide attackers with a method to determine whether a specified username exists. If the attack can be automated, it allows an attacker to whittle down a large list of potential usernames to a smaller list of confirmed usernames. This list of valid usernames for a system is extremely valuable to an attacker because it facilitates a range of other attacks including automated password guessing (brute-force) and DOS attacks. Without the user enumeration flaw to first get a confirmed list of users, these attacks become an order of magnitude more difficult.
Wallis continued: “Organisations should always seek to reduce their perimeter attack surface to a minimum, as a rule of thumb the fewer services are exposed to the Internet, the harder an organisation is to breach. Wherever services must be exposed, regular vulnerability assessments and multi-factor authentication are essential survival tools no organisation should go without.”