Symantec said the effort appeared to be driven by national spooks such as the interception of military and civilian communications.
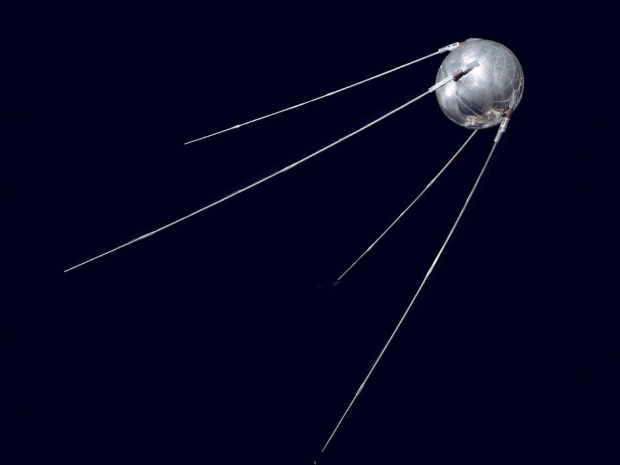
The hackers infected computers that controlled the satellites, so that they could have changed the positions of the orbiting devices and disrupted data traffic, Symantec said.
Vikram Thakur, technical director at Symantec said: “Disruption to satellites could leave civilian as well as military installations subject to huge (real world) disruptions. We are extremely dependent on their functionality.”
Satellites are critical to phone and some internet links as well as mapping and positioning data.
Symantec said the hackers had been removed from infected systems and it has shared technical information about the hack with the US Federal Bureau of Investigation and Department of Homeland Security, along with public defence agencies in Asia and other security companies.
Thakur said Symantec detected the misuse of common software tools at client sites in January, leading to the campaign’s discovery at unnamed targets. He attributed the effort to a group that Symantec calls Thrip, which may be called different names by other companies.
Thrip was active from 2013 on and then vanished from the radar for about a year until the last campaign started a year ago. In that period, it developed new tools and began using more widely available administrative and criminal programs, Thakur said.
Other security analysts have also recently tied sophisticated attacks to Chinese groups that had been out of sight for awhile, and there could be overlap. FireEye Inc in March said that a group it called Temp. Periscope reappeared last summer and went after defence companies and shippers. FireEye had no immediate comment on the new episode.
It was unclear how Thrip gained entry to the latest systems. In the past, it depended on trick emails that had infected attachments or led recipients to malicious links. This time, it did not infect most user computers, instead moving among servers, making detection harder.
Following its usual stance, Symantec did not directly blame the Chinese government for the hack. It said the hackers launched their campaign from three computers on the mainland. In theory, those machines could have been compromised by someone elsewhere.
Symantec provides the most widely used paid security software for consumers and an array of higher-end software and services for companies and public agencies.