Patrick Wardle, a former NSA hacker who now serves as chief security researcher at Synack, found the bug and told Apple about it a month ago. That gave plenty of time for Apple to fix the bug before it released High Sierra. It just could not be arsed and released it anyway. Perhaps it was assuming that every Apple fanboy would think that a Zero Day flaw was an important feature and soon everyone would want one.
Passwords are stored in the Mac's Keychain, which typically requires a master login password to access the vault. Wardle has shown that the vulnerability allows an attacker to grab and steal every password in plain-text using an unsigned app downloaded from the internet, without needing that password.
Wardle tested the exploit on High Sierra, but said that older versions of macOS and OS X are also vulnerable. Wardle created a "keychainStealer" app demonstrating a local exploit for the vulnerability, which according to the video, can expose passwords to websites, services, and credit card numbers when a user is logged in.
That exploit could be included in a legitimate looking app, or be sent by email.
"If I was an attacker or designing a macOS implant, this would be the 'dump keychain' plugin," said Wardle.
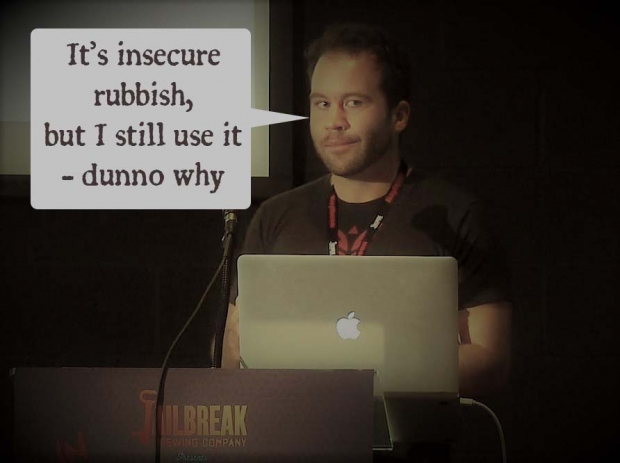
Wardle describes himself as an Apple fanboy even if it has terrible security. In fact, he even sad sorry to Apple for pointing out that something was wrong.
"As a passionate Mac user, I'm continually disappointed in the security of macOS. I don't mean that to be taken personally by anybody at Apple - but every time I look at macOS the wrong way something falls over. I felt that users should be aware of the risks that are out there I'm sure sophisticated attackers have similar capabilities."
"Apple marketing has done a great job convincing people that macOS is secure, and I think that this is rather irresponsible and leads to issues where Mac users are overconfident and thus more vulnerable", he added.
It's the second zero day bug that Wardle found for the operating system this month - the first shows how the new software's secure kernel extension loading feature is vulnerable to bypass.
Apple's answer to Wardle was that its MacOS is designed to be secure by default, and Gatekeeper warns users against installing unsigned apps, like the one shown in this proof of concept, and prevents them from launching the app without explicit approval.
"We encourage users to download software only from trusted sources like the Mac App Store, and to pay careful attention to security dialogs that macOS presents."
Apple did not say if or when it will patch the bug, but basically anyone who uploads the new macOS is vulnerable to a zero day attack that Apple so far has not been bothered fixing.