Court rules fingerprints are self-evident, but passcodes require revealing “compelling” evidence
In 2014, Virginia defendant David Charles Baust was charged with strangling and assaulting his girlfriend in his bedroom at his house. His girlfriend had admitted to hiding a video recording device somewhere in the room that was wirelessly transmitting to Baust’s smartphone. After acquiring a warrant several days later, police recovered the phone, and both the victim and the defendant admitted that Baust’s phone “could have recorded” the assault. However, the device was locked by either fingerprint or passcode.
The court’s task on CR14-1439 was to decide whether a mobile device passcode or biometric form of identification is subject to a defendant’s Fifth Amendment privilege against self-incrimination. The court ultimately ruled that “physical characteristic evidence” such as a fingerprint does not force a defendant to reveal anything new, but the presence of a unique passcode reveals testimonial evidence that requires a defendant to “disclose the contents of his or her own mind.”
“In this case, the Defendant cannot be compelled to produce his passcode to access his smartphone but he can be compelled to produce his fingerprint to do the same. […] Contrary to the Commonwealth’s assertion, the password is not a foregone conclusion because it is not known outside of Defendant’s mind. […] The fingerprint, like a key, however, does not require the witness to divulge anything through his mental processes. On the contrary, like physical characteristics that are non-testimonial, the fingerprint of Defendant if used to access his phone is likewise non-testimonial and does not require Defendant to “communicate any knowledge” at all.” (CR14-1439, p5)
No evidence for fingerprint unlocking warrants has emerged until now
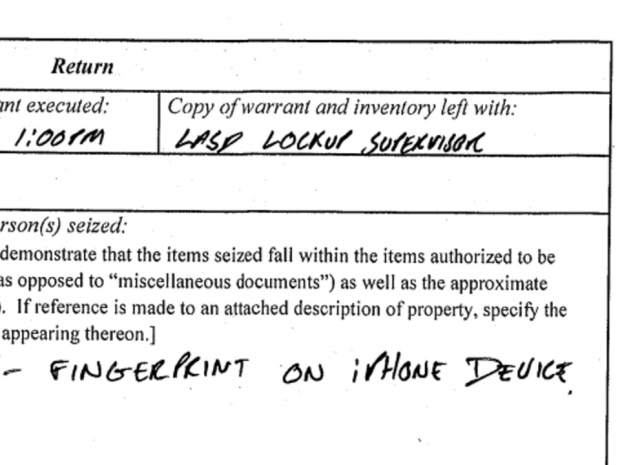
Until now, investigators and the media have been unable to reveal any criminal cases where a warrant specifically requested access to mobile device unlocking using fingerprints. While the world was being consumed with information surrounding an FBI v. Apple encryption case with a San Bernardino shooter’s iPhone, a warrant dated February 25, 2016 from the Los Angeles Police Department reveals that police quietly acquired a warrant to apply a user’s fingerprints to unlock an Apple device. According to Forbes, this is the first publicly known case in which an individual has been compelled to use a biological form of identification to unlock their smartphone.
In Case No. T6-03 98M (filed March 15, 2016), an individual identified as Paytsar Bkhchadzhyan gets her boyfriend’s home searched and is demanded to provide fingerprint access to her smartphone “within 14 days.” It is currently unknown what happened once the document was signed off – either the LAPD could have taken fingerprints directly from Bkhchadzhyan, or simply placed her finger onto the Touch ID sensor as the warrant’s wording suggests.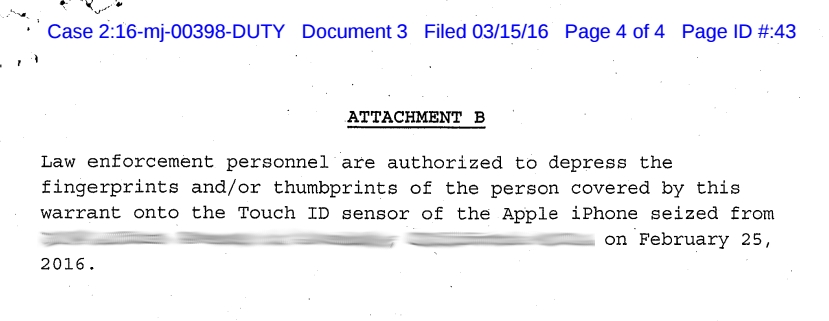
Case No. T6-03 98M (March 15, 2016) – Los Angeles Police Department (via DocumentCloud.org)
What is surprising about this case, however, is that the warrant was published outside of the U.S. state court servers, as well as outside the Public Access to Court Electronic Records (PACER) system – a website that gives the general public access to court information. Forbes journalists unsuccessfully attempted to contact the detective who signed the warrant, Apple declined to comment, the DoJ declined to comment, and the Central District of California could not be reached at the original time of discovery.
As smartphone vendors increase internal device security, law enforcement will adapt
Like the February 25th warrant case above, law enforcement agencies are now scrambling to adapt to new smartphone security metrics as vendors place more internal hardware-level security into their devices. Apple’s Touch ID-enabled iPhone and iPad units, for example, will self-lock after 48 hours of inactivity, causing some distress for police who need 5th amendment warranted access to obtaining digital evidence. This may have been the case with LAPD officials and Bkhchadzhyan’s phone.
Apple began internally software-encrypting its iPhones and iPads in 2014 with iOS, further improving basic user device protections along with Touch ID. We are now finding, however, that using the company’s fingerprint reader isn’t such a good idea for US-based individuals who want to plead the 5th.
As such, for optimal security, it is still recommended that people use a custom passcode – preferably above 4 digits (6 and higher for now) – to prevent it from being guessed by computer algorithms in certain cases. Chris Soghoian, chief technologist at the ACLU, says a short pin “let’s you use your phone like a human,” but a long passcode, while secure, “is a pain to type in” every time the device needs to be unlocked. Yet despite what critics claim, the second option of a 6+ digit numeral, word, or pattern combination – along with requiring passcode entry every time the screen is locked – is still perhaps the best option going forward in the U.S. for now.