CyberCX has been showing the interwebs how to gain access to a laptop by shorting some EEPROM chip pins with a simple screwdriver to access a fully-unlocked BIOS. Then all it took was a quick poke around the BIOS settings screen to disable any BIOS password.
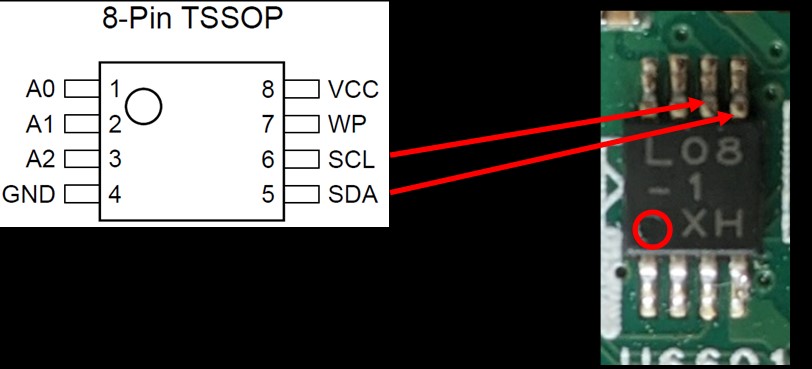
The blog shows that the easily reproducible bypass is viable on the Lenovo ThinkPad L440 (launched Q4 2013) and the Lenovo ThinkPad X230 (launched Q3 2012). Other laptop and desktop models and brands that have a separate EEPROM chip where passwords are stored may be vulnerable in the same way.
This means that all those used laptops which are sold for spares as they are practically disabled from re-use due to a BIOS lock in place are suddenly useful and any information available on them readable.
CyberCX says that some modern machines with the BIOS and EEPROM packages in one Surface Mount Device (SMD) would be more difficult to hack in this way, requiring an "off-chip attack."
The cyber security firm also says that some motherboard and system makers already use an integrated SMD. Those particularly worried about their data, rather than their system, should implement "full disk encryption [to] prevent an attacker from obtaining data from the laptop’s drive," says the security outfit.