According to a research paper with the catchy title "TRRespass: Exploiting the Many Sides of Target Row Refresh” while mitigations, collectively referred to as Target Row Refresh (TRR), is a combination of software and hardware fixes slowly added to the design of modern RAM cards after 2014 have not worked.
The team of academics from universities in the Netherlands and Switzerland said they developed a generic tool named TRRespass that can be used to upgrade the old Rowhammer attacks to work on the new-and-improved TRR-protected RAM cards.
“In this paper, we demystify the inner workings of TRR and debunk its security guarantees. We show that what is advertised as a single mitigation is actually a series of different solutions coalesced under the umbrella term Target Row Refresh", the paper said.
Researchers say that after studying all the different ways TRR was implemented by different vendors, they created TRRespass, a tool that can identify new row patterns that can be "hammered" like before.
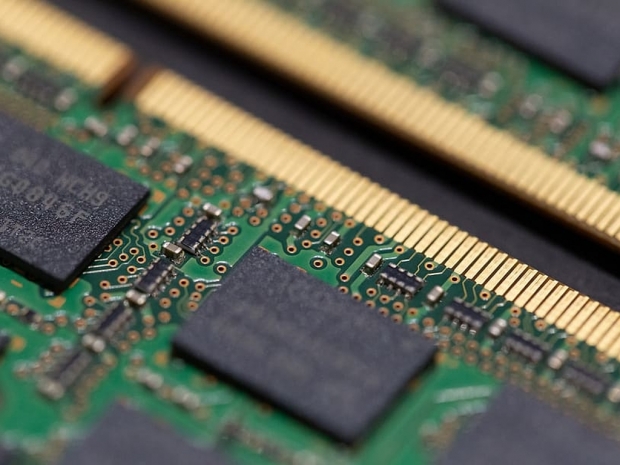
The new upgraded attacks work on both DIMM and LPDDR4 memory types, and can be used to retrieve encryption keys from memory, or escalate an attacker's access right to sudo/SYSTEM-level. "In addition to DDR4, we also experiment with LPDDR4(X) chips and show that they are susceptible to RowHammer bit flips too", researchers said.