“The United States government has demanded that Apple take an unprecedented step which threatens the security of our customers,” said Cook in an open letter titled “A Message to Our Customers” published to Apple’s website early Wednesday morning. "Opposing this order is not something we take lightly. We feel we must speak up in the face of what we see as an overreach by the US government.”
“When the FBI has requested data that’s in our possession, we have provided it. Apple complies with valid subpoenas and search warrants, as we have in the San Bernardino case. We have also made Apple engineers available to advise the FBI, and we’ve offered our best ideas on a number of investigative options at their disposal.
We have great respect for the professionals at the FBI, and we believe their intentions are good. Up to this point, we have done everything that is both within our power and within the law to help them. But now the U.S. government has asked us for something we simply do not have, and something we consider too dangerous to create. They have asked us to build a backdoor to the iPhone.”
The court order (No. ED 15-0451M), given February 16, 2016 by U.S. Magistrate Judge Sheri Pym, a former federal prosecutor, wants Apple to supply the US government with an encryption backdoor to be implemented in a custom version of iOS that will run only on the iPhone 5C belonging to Syed Rizwan Farook:
“Apple's reasonable technical assistance shall accomplish the following three important functions: (1) it will bypass or disable the auto-erase function whether or not it has been enabled; (2) it will enable the FBI to submit passcodes to the SUBJECT DEVICE for testing electronically via the physical device port, Bluetooth, Wi-Fi, or other protocol available on the SUBJECT and (3) it will ensure that when the FBI submits passcodes to the SUBJECT DEVICE, software running on the device will not purposefully introduce any additional delay between passcode attempts beyond what is incurred by Apple hardware.”
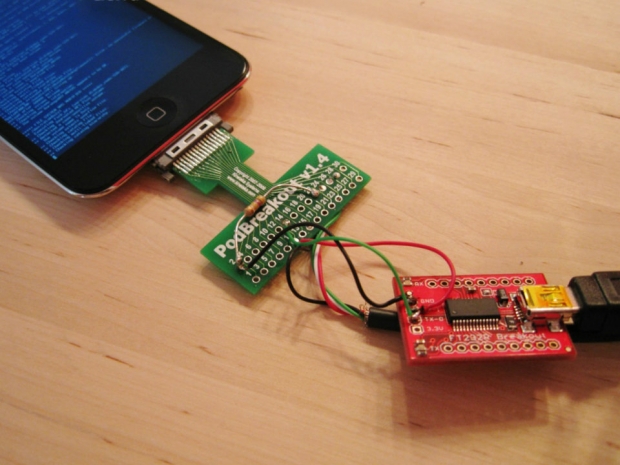
In other words, the custom iOS version ordered by the court would allow an unlimited number of password guesses to be made by the FBI without destroying any data, along with an unlimited number of PIN code guesses (via automated script) through the device’s Lightning USB port or through Bluetooth or WiFi connections. The custom iOS version would also be more likely to be loaded into the phone’s memory, rather than installed to NAND flash, similar to the way some operating systems can be booted from a USB drive.
The big problem with the way this order is written, however, is that there are no guarantees that government officials won’t be allowed unfettered access to Apple’s proprietary iOS system software code. As pointed out by ArsTechnica, the order provides no guidance on how Apple’s engineers would enable such custom restrictions, and whether or not they are susceptible to reverse-engineering by forensics experts in the future.
In October 2015 at the Wall Street Journal’s WSJDLive conference in Laguna Beach, California, the Apple CEO specifically told the audience that “no backdoor is a must,” explaining that encryption backdoors do not exclude only “bad people,” but includes all 1 billion active iPhone, iPad, Mac, iPod touch, Apple TV and Apple Watch users worldwide (numbers based on the company’s January 26, 2016 earnings report) – or roughly 13.7 percent of the world’s total population, for comparison.
"It’s in everyone's best interest that everybody is blocked out," Cook said.
Apple’s latest mobile operating system, iOS 9, accounts for 75 percent (750 million) of those 1 billion active devices, as measured by the App Store on January 11th. Only 19 percent (190 million) of active devices are running iOS 8, while the remaining 7 percent (70 million) of active devices are running iOS 7 and earlier.
With hundreds of millions of users at stake, in the US and abroad, it comes as no surprise that Cook deemed the court order “chilling” and warned that the prospects for abuse of such a backdoor are high. We all saw what happened with the catastrophic global encryption discovery in summer 2014 known as CVE-2014-0160, the “Heartbleed Bug” that exploited OpenSSL’s cryptographic software library and affected up to 66 percent of all encrypted websites.
“Once the information is known, or a way to bypass the code is revealed, the encryption can be defeated by anyone with that knowledge,” Cook explicitly warned in his open letter to customers.