The apps, most of them games, were distributed through third-party app stores by a Chinese group with a legitimate business helping Chinese developers promote their apps on outside platforms.
Check Point is not identifying the company, because they are working with local coppers but said that more than 300,000 devices were infected in the US.
The malware was able to copy popular apps on the phone, including WhatsApp and the web browser Opera, inject its own malicious code and replace the original app with the weaponized version, using a vulnerability in the way Google apps are updated.
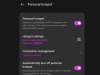
The hijacked apps work but hide the malware from users. Armed with all the permissions users had granted to the real apps, "Agent Smith" hijacked other apps on the phone to display unwanted ads to users.
Check Point's analysis and response team for mobile devices head Aviran Hazum warned the same security flaws could be used to hijack banking, shopping and other sensitive apps.
There was also a "dormant" version of "Agent Smith" in 11 apps on the Play Store, which could have been triggered into action by a banner ad containing the keyword "infect." The apps have since been removed from the Play Store, but had over 10 million downloads.