StingRay devices, or "dirtboxes," mimic local nearby cell towers and operate by forcing all nearby mobile phones and other cellular devices to connect to them. They were initially developed for the military and intelligence communities and have been used during aerial missions and can decrypt communications, allowing law enforcement to eavesdrop on conversations, emails, and text messages.
All 16 million Disneyland visitors currently fall into range of these devices, as revealed by new documents released January 27th by the American Civil Liberties Union (ACLU) and reported by ArsTechnica.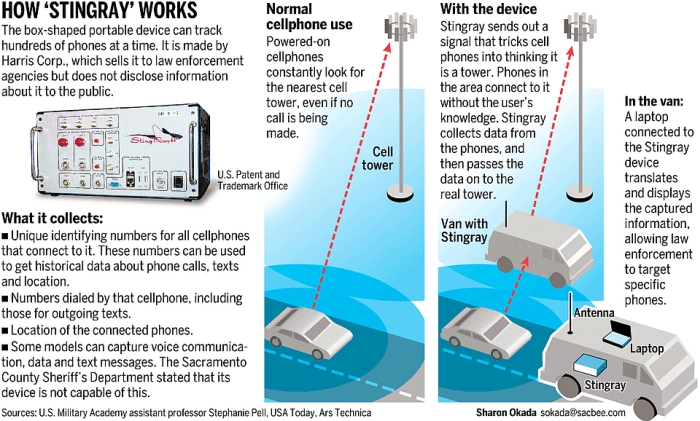
Source: Sacramento Bee
When put into “active mode,” a StingRay device will force each compatible cellular device to disconnect from its service provider cell site and establish a new connection with the StingRay. This is primarily accomplished by the device broadcasting a stronger “pilot” signal than nearby cell towers. Most current cellphone hardware operates by connecting to the nearest tower offering the strongest signal. As such, StingRay devices are meant to exploit this function in order to achieve temporary connections with nearby cellular devices.
Last year, the ACLU obtained the 464 pages of documents after it sued the Anaheim Police Department over the police agency’s failure to respond to its public records request for public phone surveillance-related documents.
According to a report by Reveal in August 2015, a DRTBox can “simultaneously break the encryption of communications from hundreds of cellphones at once. A 2011 purchase order for this equipment by the Washington Headquarters Services (a branch of the Pentagon) states the devices can retrieve the encryption session keys for a cellphone ‘in less than a second with success rates of 50 to 75 percent (in real-world conditions).’"
Pictured: StingRay II device
As the report’s title suggest, the cities of Chicago and Los Angeles have been under “dirtbox” surveillance for over a decade. One such device, the DRT 1201C, can be configured to support DF, digital voice intercept and recording, target lists of up to 10,000 entries, and up to four tuners. The device is listed in The Intercept’s surveillance catalog with the description, “Mount in an aircraft to fly over the crowd.”
“With DRT, if you put one of these on an airplane and fly them around, you can find all sorts of info about potentially thousands of people,” said Freddy Martinez, an activist who has sued the Chicago Police Department multiple times for its use of cell-site simulators. “That includes voice content, who they’re calling, what data they’re sending. It’s like a StingRay on steroids.”
Over the past three years, the veil of privacy surrounding these devices has been slowly lifting ever since the Electronic Frontier Foundation (EFF) and the ACLU originally exposed the technology during a 2012 case. As of January 1, 2016, the state of California now requires the use of a warrant for any cell-site simulator.
In fact, the US Marshals Service had been flying “dirtboxes” from five major airports across America since 2007, according to a 2014 report by the Wall Street Journal. Of course, the government says the program’s intent is to “target criminals,” but the devices can also be used to sift through thousands of other phones and unlock cryptographic keys with ease.
"Regarding using planes as cell towers, that is problematic in my opinion. It strikes me as analogous to the use of stingrays," said Brian Owsley, a former federal magistrate judge and current law professor at the University of North Texas, to ArsTechnica. "Therefore, I think the government would need to obtain a search warrant based on probable cause consistent with the Fourth Amendment. "I think the growth of the use of drones will further exacerbate this problem," he added.

